Event Recap: 2022 Cybersecurity Policy Priorities
Perspectives from the Executive and Legislative Branches
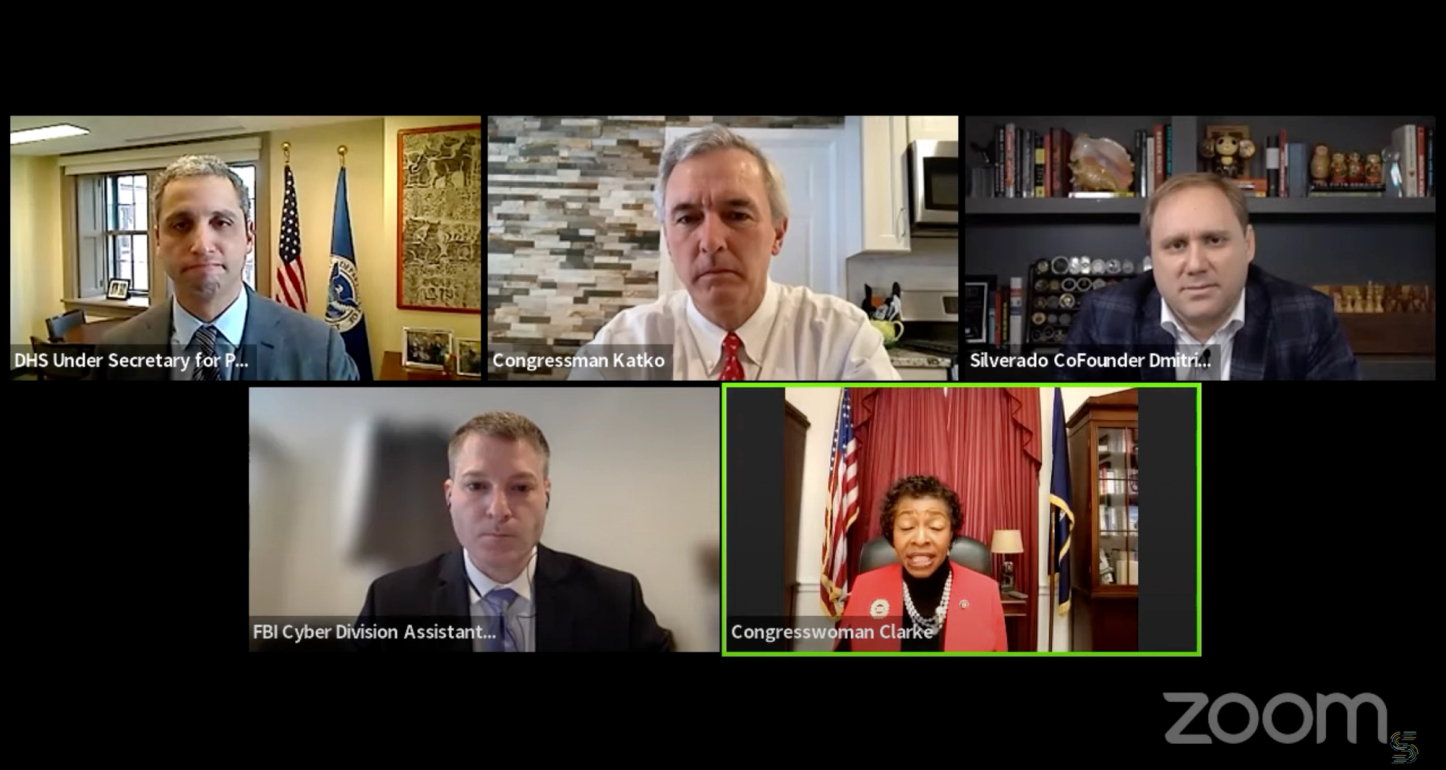
Silverado Policy Accelerator hosted a virtual event on Thursday morning exploring key cybersecurity policy priorities for the coming year, with perspectives from the legislative and executive branches. The discussion, moderated by Silverado’s Executive Chairman and Co-Founder Dmitri Alperovitch, featured Congresswoman Yvette Clarke (D-NY), the chair of the Homeland Cybersecurity, Infrastructure Protection and Innovation Subcommittee, Congressman John Katko (R-NY), the ranking member of the House Homeland Security Committee, U.S. Department of Homeland Security Under Secretary for Policy Robert Silvers, and FBI Cyber Division Assistant Director Bryan Vorndran.
The panelists laid out a range of priorities for the coming year, including new steps to strengthen the Cybersecurity and Infrastructure Security Agency (CISA), combat ransomware, and pass cyber incident reporting legislation. Congresswoman Clarke and Congressman Katko agreed that passing cyber incident reporting legislation, which was not included in the FY 2022 National Defense Authorization Act, should be a top priority for the current Congress, and both members expressed confidence that Congress will be able to find a vehicle to pass that legislation within the year. Congressman Katko also noted that he hoped to turn CISA into a “$5-billion agency,” which would double the agency’s current budget.
On the executive side, Under Secretary Silvers and FBI Assistant Director Vorndran discussed the precise mechanism of an incident reporting system, with Assistant Director Vordran saying that the FBI needs “real-time and unfiltered” access to the data gathered through that system in order to respond to effectively incidents, even if the reports are filed directly with CISA. Under Secretary Silvers indicated that CISA plans to share all data directly with the FBI even if the final legislation does not specify an explicit information-sharing mechanism.
A full transcript of the event is available here, and a complete video recording is available here.
Pillar
Cybersecurity
Great Power Competition